Learn to navigate the intersection of law, technology, and business. This program covers information security governance, enterprise risk management (ERM), compliance frameworks (ISO 27001, SOC 2, NIST CSF), cyber laws (IT Act 2000, GDPR, HIPAA, PCI DSS), audit methodologies, and incident response readiness.
✔ 50% practical case studies • 15+ compliance projects • Official‑style practice exams • Capstone project (enterprise GRC framework implementation) • 24/7 access to templates and tools.
Policy drafting, risk assessment (qualitative/quantitative), control design & testing, internal audit, regulatory mapping, third‑party risk management, breach notification, legal advisory, and remediation planning.
Basic understanding of information security concepts. No legal background required – we cover cyber law from fundamentals.
Draft a complete information security policy suite, conduct a risk assessment for a fintech startup, build a GDPR compliance roadmap, and simulate an internal audit against ISO 27001.
Exam vouchers, mock tests, resume review, portfolio building, and interview preparation for GRC Analyst, Compliance Officer, Internal Auditor, and Cyber Law Consultant roles.
Tailored GRC upskilling for compliance and audit teams
Choose from ISO 27001 Lead Implementer, CISA, CRISC, or Indian Cyber Law tracks.
Access editable templates for policies, controls, risk registers, and audit checklists.
Monitor progress and skill gaps with detailed analytics and competency mapping.
Volume discounts for teams of 10+, plus pay-as-you-go options.
Dedicated GRC experts to assist your learners with real‑world scenarios.
Single point of contact for seamless training delivery.

Get a custom quote for your team's compliance and risk training.
From Legal Frameworks to Enterprise Compliance Automation
Interpret the Indian IT Act 2000 (amended), GDPR, HIPAA, PCI DSS, GLBA, and emerging AI regulations. Understand data localization, breach notification, and cross‑border data transfer rules.
Establish governance structures, define security charters, align with business objectives, and manage board‑level reporting.
Perform risk identification, analysis (qualitative/quantitative), risk treatment, and risk monitoring. Use frameworks like ISO 31000, NIST RMF, and FAIR.
Implement ISO 27001, SOC 2, NIST CSF, COBIT. Conduct internal audits, manage evidence collection, and drive remediation.
Assess vendor security posture, draft due diligence questionnaires, and manage supply chain risks.
Write enforceable policies (AUP, BCP, data classification), manage security awareness programs, and handle legal aspects of incident response.
Ideal Candidates for Cyber Law & GRC Certification
Designed for professionals in IT, security, legal, audit, and business management. No legal background is required – we start with fundamental cyber law concepts. This program bridges the gap between technical security controls and regulatory compliance, giving you the confidence to pass examinations like CISA, CRISC, ISO 27001 Lead Implementer, and Indian Cyber Law certifications. Average salaries for GRC specialists in India range from ₹8 Lakhs to ₹22+ Lakhs per year.
Your Step‑by‑Step Path to GRC Mastery
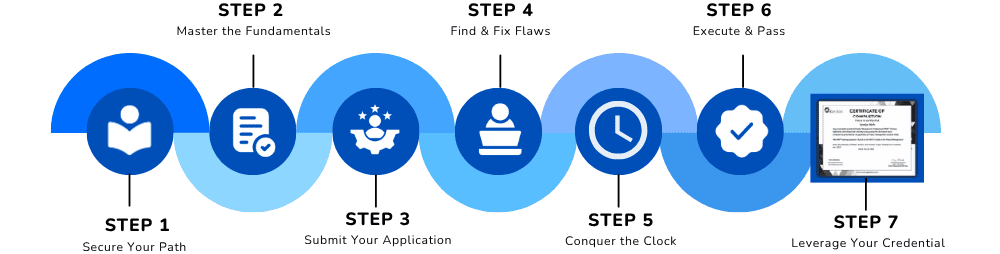
Understand governance structures, risk management frameworks, and the legal environment for cyber security.
What You Need Before You Start
Objective: To certify your ability to design, implement, and manage governance, risk, and compliance programs in alignment with laws and standards. Candidates should have:
Understanding of common security controls (access control, encryption, backup) is helpful but not mandatory.
Ability to read legal texts, write policies, and structure risk assessments.
No prior GRC experience required — we start with fundamentals and gradually cover advanced compliance automation and auditing.
Comprehensive modules covering cyber law, governance, risk, and compliance frameworks
Understand key sections, cyber crimes, data protection obligations, intermediary liability, and adjudication.
Compare compliance requirements, data subject rights, breach notification timelines, and penalties.
Create security charters, define roles (CISO, DPO, compliance officer), and align with business strategy.
Draft enforceable policies (Acceptable Use, Access Control, BCP, Data Classification).
Risk identification, analysis, evaluation, treatment, and monitoring.
Perform asset‑based risk assessments, scenario analysis, and calculate Annualized Loss Expectancy (ALE).
Implement an Information Security Management System (ISMS), Statement of Applicability, and risk treatment plan.
Map controls to security, availability, processing integrity, confidentiality, privacy; use CSF tiers and profiles.
Plan, conduct, report, and close audit findings. Use audit checklists and sampling methods.
Use GRC platforms (Vanta, Drata, AuditBoard) to automate evidence collection and control testing.
Conduct risk assessments, request evidence (SOC 2, ISO 27001), and evaluate criticality.
Include data protection, breach notification, and audit rights in contracts. Perform continuous vendor monitoring.
Conduct DPIA, maintain records of processing, and design privacy notices.
Navigate breach reporting timelines, communicate with regulators, and coordinate with legal counsel.
Computer offences, cyber fraud, IP theft, cyber terrorism; Indian and cross‑border jurisdiction.
Principles of forensic soundness, seizure, preservation, and legal admissibility of electronic evidence.
Create business continuity plans, test strategies, and integrate with risk management.
Design effective training programs, phishing simulations, and measure culture change.
Design a complete GRC program for a mid‑sized organization: policy set, risk register, control matrix, audit plan, and breach response playbook.
Practice with official‑style questions for CISA, CRISC, ISO 27001 Lead Implementer, and Indian Cyber Law certification exams.
Lifetime Access
Real GRC Projects Included
Mentor Support
Practice Assignments
Certificate Preparation
Join 11,000+ successful GRC and compliance professionals who transformed their careers with our industry‑aligned training. Cyber law and GRC skills are essential for every modern organization.
✅ Limited seats available for the upcoming batch • EMI options available • Includes policy templates & audit checklists